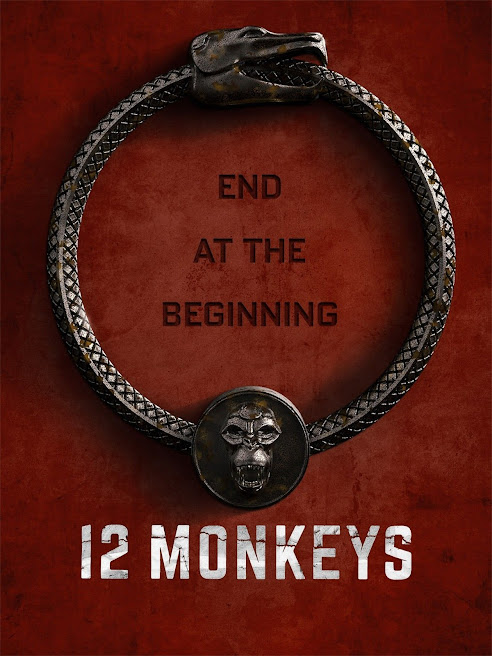
The 12 Monkey Lies, Relationships and Marriage
1234
4
There is not something wrong with you if you are having a hard time making a relationship, love or marriage work. Partly it is because you have been taught lies about love by media, TV, movies, books, psychologists, psychiatrists, friends, parents, spouses, teachers, advisors and others some of whom probably had more trouble than you. About 2600 years ago the Greek story teller Aesop was reputed to have said “Never trust the advice of a man in difficulties.” To that we should add “or a woman.”
Love doesn’t have to be so hard. Anything is hard or impossible to make work if you don’t know how it works. If you were trying to fix your car and knew nothing about cars it would be impossible.
Here is the good news. My wife and I have professionally counseled couples and individuals about love, relationships and marriage for almost 50 years each. Many times couples or individuals have come to us where we thought there is no way we can keep this marriage or relationship together. They are fighting so much. They seem so mismatched. Maybe they should separate or divorce. But despite that we put our own ideas aside and continued with the intention that we will keep them together, used techniques we have learned over the years that worked, and saved countless marriages and relationships. Now 20 or 30 years later there are some we are still in communication with and they are still together and getting along well. Our counselors use the techniques we have been using successfully.
One of the most important things for us to do is find out what lies they believe and offer them true data. We know the misery divorce and breaking up can be and the joy that love and creating a family can be. We don’t want you to have to experience that suffering or if you are suffering now we want to help you through it. We like happy relationships and families. We want that for you. It is possible. Now something can be done about it.
What you don’t know is hurting both of you. Let’s start by telling you what some of the other lies you have been exposed to are.
4
Big Lie #1:
Love is really hard.
STORY AT-A-GLANCEThere is not something wrong with you if you are having a hard time making a relationship, love or marriage work. Partly it is because you have been taught lies about love by media, TV, movies, books, psychologists, psychiatrists, friends, parents, spouses, teachers, advisors and others some of whom probably had more trouble than you. About 2600 years ago the Greek story teller Aesop was reputed to have said “Never trust the advice of a man in difficulties.” To that we should add “or a woman.”
Love doesn’t have to be so hard. Anything is hard or impossible to make work if you don’t know how it works. If you were trying to fix your car and knew nothing about cars it would be impossible.
Big Truth #1
First the bad news. Despite all the advice, education, books, talk shows, tabloid advice, sexual freedom, preaching, social attitude change it is still true that about 50% of marriages in the US end in divorce. That is not fun for husbands, wives or children.Here is the good news. My wife and I have professionally counseled couples and individuals about love, relationships and marriage for almost 50 years each. Many times couples or individuals have come to us where we thought there is no way we can keep this marriage or relationship together. They are fighting so much. They seem so mismatched. Maybe they should separate or divorce. But despite that we put our own ideas aside and continued with the intention that we will keep them together, used techniques we have learned over the years that worked, and saved countless marriages and relationships. Now 20 or 30 years later there are some we are still in communication with and they are still together and getting along well. Our counselors use the techniques we have been using successfully.
One of the most important things for us to do is find out what lies they believe and offer them true data. We know the misery divorce and breaking up can be and the joy that love and creating a family can be. We don’t want you to have to experience that suffering or if you are suffering now we want to help you through it. We like happy relationships and families. We want that for you. It is possible. Now something can be done about it.
What you don’t know is hurting both of you. Let’s start by telling you what some of the other lies you have been exposed to are.
Big Lie #2:
You fall in love and out of love by accident. It just happens.
STORY AT-A-GLANCE
Relationships, love and
marriage are things you CREATE like a great meal or a work of art. YOU
can learn how to cause them. It all starts with your decision.
Big Truth #2
They don’t just happen to you. Falling
“out of love” is a LIE. The truth is a relationship (or a marriage) is
something YOU create and when you stop creating it, stop deciding to put
it there, it ceases to exist. This is true whether it’s just a day into
a relationship, a year into it, a decade or a lifetime.
It is likely that a couple did something to create a marriage to
begin with or somewhere during it. Maybe they fell in love and had a
wonderful romance, or they showed up in church for a wedding, or got a
license at the courthouse, or moved in together or just started having
sex. If the relationship is now in trouble, it is because instead of
continuing to CREATE it, people are expecting it to run on automatic —
like a self driving car. The TRUTH is they simply stopped working at it
and the relationship ceased to exist!
This is a fundamental Big Lie not
only about love, relationships, sex and marriage but about Life in
general. It includes the idea or attitude that things (good or bad) just
happen to you without you having anything to do with causing them. Many
people go around thinking they are a victims of life and so stop
trying. Sure, there are plenty of random things that can happen in life.
You could have a building fall on you in an earthquake or finally win
that lottery. But, love — you cause that. You might have forgotten how,
but the truth is you cause your emotions; they come from you. You cause
falling in love and you help someone fall in love with you.
If you know this, if you can accept this or begin to think with this
understanding, then you have a tremendous advantage– not only in
relationships but in life.
So, what do you do when the passion is gone and you just feel
annoyance or anger, anxiety or depression or hopelessness about a
relationship (or even about life in general)? What if you feel you just
can’t create it anymore? That there have been too many fights, or you
feel you have hurt the other person too much; or maybe you feel you have
been hurt too much? Maybe you have the added burden of too many secrets
from each other and now you can’t even remember why you ever liked this
person in the first place. That can feel pretty bad. It can seem
hopeless.
Ideally you can have personal marriage counseling with someone who
understands marriage, relationships and the mind really well, unlike
pill pushing quacks. I’m here to assure you there are actual proven,
reliable procedures that are used every day to put a relationship back
together; even sometimes better than it was in the first place!
That is what we do.
But you don’t know us…yet.
You should not jump in at the deep end but instead just get your feet
wet at first. We can get to know each other and see if we think we can
work together successfully.
And here are some things you can try on your own:
- Decide you are creating a good relationship. You may have to decide this many times until you believe it.
- Push aside or push THROUGH any hurt feelings or injured pride or
whatever negative feelings may be getting in your way and start creating
the relationship again. Don’t wait for divine intervention or fate or
something like that to bring the two of you together. Start creating it.
Do something to make it better. The easiest way is to just help your
partner in some way that he or she likes. Your friendly expert counselor
can help you find something you can do successfully.
- If you can’t even talk to each other because every conversation
turns into a fight, do your best to STOP mid-fight (preferably BEFORE it
turns into a fight) and take a walk around the block. This is so simple
and easy that it is hard to get people to do it. And if you can get
your partner to walk around the block in the opposite direction that
works even better. Once you’re walking, keep walking and looking at the
environment until you both feel better and your attention is no longer
fixed on the quarrel, and instead is turned outward, onto your
surroundings. It may sound too simple to be workable, but this simple
remedy can give you and your partner some relief and even possibly a new
and better perspective on the relationship.
- Stop dwelling on (thinking about or stressing about) all the things
that are wrong with the relationship for a while. Stop trying to point
out what’s wrong to your partner and just stop talking about anything
like that for now. The end result of all that upset, thinking and
worrying is more upset, thinking and worrying. And the end result of
talking about it all when upset or anxious or depressed is likely to be
MORE fighting!
Instead, remember some things the two of you like to do together.
Pick one of them and do it again. What do you like to do together? Do
you like going shopping or a sport or going to the beach? Great. Go
shopping or go to the beach or your favorite sport (or whatever is good
for you both) and don’t discuss the relationship. Just have fun. (But
don’t pick a dangerous sport like mountain climbing when you are upset.)
Before you were upset with each other, you liked each other, you
agreed with each other on various things and so you were able to
communicate with each other to some degree. But here’s something that
may be new news: The more you liked each other (and agreed with each
other and communicated with each other) in the past, the more upset you
are in the present when those things break down.
You possibly have had a disagreement with someone you did not like
much in the first place or never really agreed with or talked to much.
That may bother you briefly but most likely you just moved on. When we
get really upset with someone and stay upset, it is actually a sign of
how much we really liked them in the first place.
To summarize: don’t dwell on everything that is wrong but put the
fundamental fun back into being together and doing things you both like
without discussing what is wrong over and over. After you have put the
fun back in it may not seem so serious after all.
The above can all help, but it is important to be able to talk to
someone friendly and not judgemental who can really understand you.
There is more you need to know to completely repair a relationship or a
love or a marriage.
There is a tested science of successful relationships that gets
proven and predictable good results. You can talk with a trained,
friendly, expert counselor who knows and is skilled in applying these
techniques, one who will listen, understand and advise you about your
unique situation.
Big Lie #3:
When you fall out of love it can never be fixed and it is time to move on.
STORY AT-A-GLANCEIt is true you can’t fix it if you don’t know how. That applies to almost anything. But you can learn how and it is not that difficult when you understand the problem and know how. It is far more satisfying to fix it than to give up.
Big Truth #3
This is a big one that is published continuously in movies, TV, soap opera, online, tabloids, gossip magazines and by so-called experts. Don’t believe that garbage. They write the most alarming clickbait lies they can get away with because that is what they get paid to do. The more sensationalism, the more clicks, the more clicks, the better the sales through ads. It is a vast understatement to say these people are not experts on life. They may be experts on getting you to click on their links. Their careless lies, told with reckless abandon, do nothing but ruin lives and wreck families. I don’t think you would purposely destroy a marriage or a family. Don’t let it happen to you.The Truth is, love is something that you both create. See Big Lie #1 above. The hopeful note is that love can be recreated better and more sensibly than ever. You can get past your history and learn how to be happy again. Over and over we have counseled couples whose relationships and marriages seemed doomed and with honest work on their parts, gotten them back together. Sometimes in as little as a few hours! And it was no temporary fix because we have stayed in communication and decades later they are still together.
There is a tested science of successful relationships that is proven to get predictably good results.
To experience this for yourself, you can talk with a trained, friendly master counselor who knows and can skillfully apply this science, someone who will listen, understand and advise you about your unique situation.
Big Lie #4:
I am angry / upset / sad because of what you just said or did.
STORY AT-A-GLANCEThis may be true but if the upset continues the chances are you are upset because of something happened earlier that you don’t know all about. You can find it and be happy again.
Big Truth #4
If saying what it is that upset you did not make you feel at least somewhat better that is probably not the actual reason you are upset. When you find the real reason for feeling sad, angry, anxious or upset you will begin to become happy again. The real source of a lasting upset is almost always EARLIER. It may have nothing to do with the person you are upset with now. It may come from earlier this lifetime or even before.Locating the actual source of the upset requires personal counseling. It is not likely something you are likely to find by yourself. It is hidden by unconsciousness. The more you think about it the more introverted you may become which leads to more thinking, pondering, worrying, irritation and depression.
There are some things you can know about it. Recognize your upset is from SOMETHING THAT HAPPENED EARLIER that is partially or wholly unknown to you.
Do something to get your attention extroverted. Take a walk and look at the environment. Or exercise. Or do something creative. Usually thinking about why you are upset just leads to more thinking and introversion and solves nothing.
There is a type of personal counseling that does actually get to the root of these upsets and releases you from their grip. It does not take years. It takes hours. You can be happy again. You can do it. There is a tested science of successful relationships that gets proven predictable good results. You can talk with a trained friendly master counselor who knows and is skilled in applying this science, who will listen, understand and help you find the source of your upset and be free of it. This is not done by counselor telling you where it is from. The counselor helps you to look. The real answers lie within you.
Big Lie #5:
If I am depressed, anxious or angry about my relationship a drug will fix it.
STORY AT-A-GLANCEChemicals will not cure a broken heart. Pharmaceutical and street drugs and alcohol can be addicting and make it more difficult to recover. You can be happy again without ingesting drugs or alcohol.Big Truth #5
This lie makes $70 billion a year for the pharmaceutical industry but cures nothing. They spend billions in advertising including payoffs to doctors to support this lie. If you take Vicodin or morphine after a surgery, you won’t be in so much pain. Painkillers are often needed for a short time. But taking psychiatric drugs will not cure a broken heart. They can make you unfeeling and addicted, harm your health, family, relationships and life. They are addictive and withdrawal can be a life threatening hell.These drugs also make it difficult or impossible for counseling or therapy to work because patients who use these drugs lose the ability to have the realizations (also known as aha moments, cognitions, epiphanies) that can change her or his life. The drugs do not cure anything but instead add another layer of unconsciousness that prevents discovering the real sources of depression and anxiety and vanquishing them. These feelings can be erased permanently but not while on psychiatric drugs. You can be happy again without them.
The best thing to do is not get on psychiatric drugs in the first place. If you are on them and choose to stop, you should work with a cooperative enlightened medical doctor to get off them. We are not medical doctors and do not give medical advice. If there is an addiction we can refer you to very effective drug rehabs. Drugs and alcohol are a huge barrier to having a good relationship. Among other things they inhibit the ability to love, feel, reason and have emotions, both positive and negative. Here is a not approved by Big Pharma link with more information www.DrugFreeWorld.org/. Alcohol and drug use have destroyed countless relationships for centuries.
Now you can get relief without drugs and build a better relationship. There is a tested science of successful relationships. It results in happier, more stable relationships. You can talk with a trained friendly Master Counselor who knows and is skilled in applying this science, who will listen, understand and advise you about your unique situation.
Big Lie #6:
He or she is the only one for me, is my soulmate, completes me. I will never have as good a partner again, etc.
STORY AT-A-GLANCE.There are probably around 500 million people on Earth in your age range of the opposite sex. There is more than one for you but you have to be able to decide that he or she is The One. There is a way to be able to do this.Big Truth #6
That is a nice romantic fairy tale that does not happen to be true. There can be love and passion and excitement and understanding with more than one of them. If there was only one you would have a better chance of winning the lottery than having a happy relationship. However you can decide or realize that someone is the right one for you, that you are in love with that person and that you are married for life and make it happen.It is obviously true that some couples are more suited for each other than others. Some possible deal breakers are: If one of you is dynamic and enthusiastic and the other is pessimistic and hopeless about life it is not likely to work out. If one wants children and the other does not that is likely to cause problems. If one wants lots of sex and the other has no interest that would be a problem. If you have only sexual attraction but really don’t like each other it won’t last long unless you get to know each other better and find out you do like each other and agree about more than sex. If one of you does not like to talk and the other is gregarious this can grate after a while. If a partner is a drug addict, alcoholic or chronically physically or mentally abusive that is a big problem.
Much of this can be overcome if the desire to do so is there and there is sufficient love, then you can reach agreement on things and have enough communication.
The best thing is to get to know each other well before you commit. And when you decide, decide for life, not until someone more attractive comes along. And then continue to create the relationship. Many people have difficulty deciding their partner is The One. For one thing they wait to be struck by lightning or something else to happen to them that will make up their mind for them. Another barrier to being able to decide is that you have had too many losses in your relationships or have made too many wrong decisions. Having been false to another or having harmed someone in a relationship could lead to losing your own ability to trust or decide. If you lived through bad relationships between your parents or witnessed bad relations between others, that can make you doubtful and suspicious. Fortunately there are now ways to clear away these problems so you can continue to make up your mind with certainty and create the relationship despite momentary upsets, uncertainties and temptations.
I know couples who decided to get married after a few days and stayed very successfully married for life. It does not have to take a long time to decide. Just look, ask, listen and see what you see and hear what you hear from your potential mate. Make sure there is more alignment of what you want in the future than conflict. Then it is YOU who decide that you are all in and he or she is The One for you. You just intentionally decide it or know it. Remember, it doesn’t just happen to you. You create it. See 2 above.
There is a tested science of successful relationships that gets proven predictable good results. You can talk with a trained friendly master counselor who knows and is skilled in applying this science, who will listen, understand and advise you about your unique situation. She or he can help you assess whether the two of you are suited or not. The counselor will only help you look, not tell you what you must do. That is up to you.
Big Lie #7:
It is all about sex. Waiting for the perfect orgasm.
STORY AT-A-GLANCESex gets better with better communication. Despite what you see in movies and TV people who are depressed or anxious or angry do not generally have good sex. Sex is not the basic human motivation and does not determine your long term emotional state. There are effective ways to improve communication between couples and have more happiness. Then better sex is possible.
Big Truth #7
Actually the better you get to know your partner, the more you like each other, the more you are in agreement about the important things in life, the more communication you have with each other the better the sex can be. It actually can get better as you get older if you keep creating and improving the relationship. Sex sells and can be fun and is very interesting but it is not all there is. Freud, the Father of Modern Psychology “believed that all tension was due to the build up of libido (sexual energy) and that all pleasure came from its discharge.” This is false. There are many things in life that give pleasure other than sex. High on the list are helping another, creativity, being who you really are, accomplishing what you set out to do, having what you need and want.There is a tested science of successful relationships that gets proven good results. You can talk with a trained friendly Master Counselor who knows and is skilled in applying this science, who will listen, understand and advise you about your unique situation. He or she can help you move to the next level and to be able to create a happy loving relationship that is based on more than sex.
Big Lie #8:
I have trouble with relationships and that is why I am unhappy.
STORY AT A GLANCENo, you probably have trouble with relationships because you are unhappy. Fix yourself first. You could have a loss of someone you love and that would certainly make you unhappy. But if your general emotional state is depressed or anxious or angry you will have trouble generally in life including relationships. Love, relationships and marriage are part of life. Your life and emotional state need repair. This can now be done.
Big Truth #8Often people blame their partner or the state of their relationship for how they feel emotionally. If one feels antagonistic, angry, anxious or depressed they tend to blame it on the person they are around. Your partner may have nothing to do with the upset or only remind you of someone you were upset with earlier. Of course this upsets your partner who wonders why you are upset with him or her all the time and things go downhill from there.
Would you want to have a relationship with someone in the emotional state you are in? If you are not sure you need to fix yourself first. This could be a great relief both to you and those who care about you.
There is a tested science of successful relationships that gets proven good results. You can come up to the present and out of the past appreciating the person in front of you. Talk with a trained friendly Master Counselor who knows and is skilled in applying this science, who will listen, understand, help you and advise you on a program so that you can be happy again.
Big Lie #9:
My unhappy emotions are me and if you love me you will accept me the way I am.
STORY AT A GLANCEYou are innately happy, healthy, loving, communicative, intelligent, energetic, courageous, responsible, friendly, likable, able, successful, capable of high interest in and love for the opposite sex without all the drama. That is the real you. You can be yourself.
Big Truth #9
This idea that you are your negative emotions used to seem true before modern advancements in the subject of the mind. You are not those emotions that cause you and those you love so much heartbreak. Those unwanted emotions, anger, upsets, anxieties, depressions are added to the real you. They come from mental image pictures of past bad experiences. The harmful effects of these pictures can be permanently erased. Sometimes people compulsively act like those who hurt them. You can be freed from those compulsions. You are basically good.
There is a tested science of successful relationships and life that gets proven good results. Talk with a trained friendly master counselor who knows and is skilled in applying this science, who will listen, understand and get you started throwing off the shackles of the past and freeing the real you.
Big Lie #10:
I have been depressed and sad since the break up or loss and I will never get over it.
STORY AT-A-GLANCEThere has been a breakthrough and that may be hard to believe but you can recover from a loss, a break up, loss of a loved one in hours, not years. You can be happy again and start fresh.Big Truth #10
It is difficult to convince people who are hopeless that they can have hope and even be happy again but using these techniques we have counseled people on the loss of a husband or wife through death or divorce and seen a recovery in a matter of hours or weeks, not months or years or never. These terrible losses can devastate a whole life and often do. This is one reason the death of one spouse is often followed by the death of the other. Now the person who has had the loss can move on, remembering the good things about their mate without the sadness, recovered from the loss and able to start fresh and optimistic. This could happen for you or a loved one. No drugs or medications are used. We will start with a consultation to assist in recovery and map out a program to free you from your grief. Included with your counseling are video(s) and/or book(s) chosen for you to help you understand what is happening to you, what can be done about it and give you a way to survive it and recover to a better condition than you were in before.
There
is now a science of human behavior that can help you decide whether
that person you might have a relationship with or are in love with or
married to is likely to be faithful to you, will be a good father or
mother, will help you succeed in life or drag you down. If you two are
not a good match now we help both of you improve so you are happier,
better matched and you can rationally decide where to go from there.
You may find that you are the one who needs improvement most. Now something can be done about it. When the actual situation that is messing up your life is discovered, then we will make a plan to effectively deal with it.
Using this science a friendly master counselor will ask you questions, listen, understand, help you evaluate the person you are thinking about and make a rational plan.
You may find that you are the one who needs improvement most. Now something can be done about it. When the actual situation that is messing up your life is discovered, then we will make a plan to effectively deal with it.
Using this science a friendly master counselor will ask you questions, listen, understand, help you evaluate the person you are thinking about and make a rational plan.
Big Lie #12:
It’s okay to cheat.
STORY AT-A-GLANCECheating is THE major cause of marriage and relationship upsets, breakups and divorce with those we counsel. Cheaters have many justifications. They are just excuses. Don’t do it. If it happened there is still a good chance we can help repair the relationship
Big Truth #12
In marriage counseling it comes up over and over. Even where the infidelity was 10 or 15 years ago before they get married the trust has not fully returned. The love they shared is not as much. The communication is not so wonderful as before. This leads to anxiety, depression and a stressful relationship. The moment’s pleasure does not outweigh the mental pain you may have for years. Infidelity often leads to divorce. The effects of divorce are often devastating for the couple as well as the children. Long-lasting sadness and less successful lives for all is often the result as well as lives of financial struggle for the mother, father, and children. Think of that next time you are tempted.A marriage or relationship is something you create. It doesn’t just happen to you. A husband and a wife create a future together for themselves and often children. If they continue to create it together this can lead to a great deal of happiness, fulfillment and success in life. If it becomes a game of husband versus wife it leads to depression, anxiety, despair and failure.
If you are so inclined to consider the possibility of future lives you can look at it this way. In this life you chose to play this game. It is you, your mate and your children versus the counter intentions and harmful actions from some others in a not very sane world. You and your mate and children are on the same side in this war. If you have an affair you are committing treason against your family who are your allies in this war. You may believe in future lives or heaven or whatever. There is an eternity of future and in that eternity there may be future romance, adventure, sexual sensation, mates and children. There is no scarcity. Just do what you are doing when you are doing it. In other words create the relationship with the partner you are with now.
I was flying across country next to a wise and kind woman who had been a school teacher for 40 years or so. We were trading stories about teaching children. She told me “There are two kinds of children. There are children who have parents and children who don’t.” By that she meant the children who come from what used to be called good homes are happier, do well in school, succeed in life. And those who come from a family where one or both parents are missing or physically present but not being parents don’t do so well. With rare exceptions where the child becomes the adult in the family that is the case. Those kids rise to the ocassion but they have a hard time too. Children need parents. They came into this world expecting parents to be parents and be grown ups. Think of your kids next time you are tempted. Be the grown up. Set a good example for your children.
If you have already been in a relationship harmed by cheating, don’t despair. Now, something very effective can be done about it in a surprisingly short amount of time. We use breakthrough techniques that actually can restore the love, communication, agreement, and trust and often make the relationship better than before.